10/13: Securing Containerization
Containerization has transformed software development by making applications more portable, scalable, and efficient. Tools like Docker, Kubernetes, and Podman have become standard in modern DevOps pipelines. However, as containers proliferate across environments, so do the security risks associated with them. Securing containerized applications isn’t just about protecting individual containers — it’s about safeguarding the entire […]
40

MIX
10/5: Early Cloud Adopters
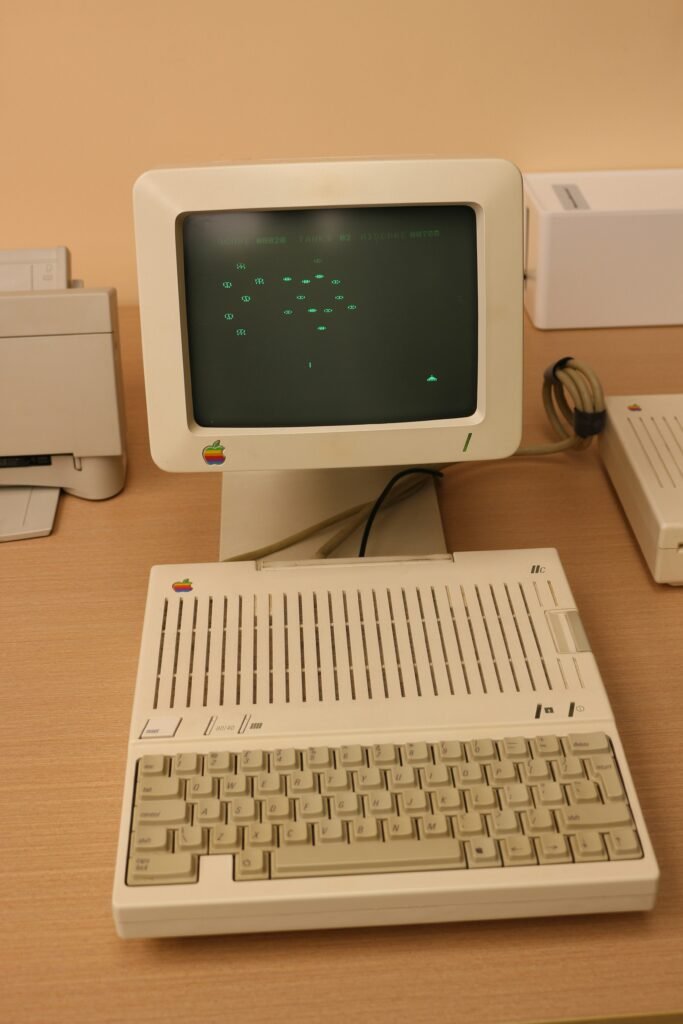
When cloud computing first emerged in the early 2000s, few organizations were willing to hand over their data and workloads to someone else’s servers. Yet, a handful of visionary companies saw the potential of on-demand, scalable infrastructure and became the first cloud customers—paving the way for the global cloud ecosystem we know today. The Dawn […]
39

Mix https://www.pearltrees.com/ryeoverly Mix
9/28: Cloud Storage

Cloud storage solutions are no longer just about convenience—they are critical infrastructure. With enterprises moving sensitive workloads to the cloud, the robustness of security measures has become a decisive factor in adoption. Protecting data requires layered defenses, advanced cryptographic practices, and continuous compliance. Below is a closer look at how modern cloud providers secure their […]
38
Mix Flipboard
9/21: IAC

As organizations scale their cloud and hybrid environments, manually configuring servers, networks, and services becomes a bottleneck. Infrastructure as Code (IaC) addresses this challenge by treating infrastructure the same way we treat application code—declarative, automated, and version-controlled. Declarative vs. Imperative Models IaC generally follows two models: Declarative: Engineers define the desired state of infrastructure (e.g., […]
37

Mix FLipboard
New codebase (UGC)

Homepage (react) Profile (react / tailwind) Discover (react / tailwind) Create (react / tailwind) Messaging (react / tailwind)
9/14: AI Production Workflows

Artificial Intelligence (AI) has rapidly moved from research labs into everyday business applications, powering everything from recommendation engines to fraud detection. But developing an AI model is only part of the journey. The real challenge lies in production workflows—the processes that take AI from experimentation to scalable, reliable, and secure deployment. Building a proof of […]
